Stainless Steel Insulated Barrels Stainless Steel Insulated Barrels,Stainless Steel Thermos Food Containers,Stainless Steel Drum With Lid,Stainless Steel Drum Jiangmen Junerte Stainless Steel Kitchenware Co.,Ltd , https://www.jmjetkitchenware.com
Recently, the Security Research Laboratory found that some payment security systems in Germany and some European countries have neglected some basic principles and best practices of security. They cannot guarantee the security of customer data and are vulnerable to financial fraud by attackers.
Experts at the Security Research Laboratory say that many of Germany's payment terminals use older versions of the 1990s that have long been proven to be vulnerable, and that there are problems with data encryption.
According to the researcher, because the payment systems in these countries use the old version of the agreement, the vulnerabilities exist between the cashier and the PoS, and on the other hand, in the process of transferring data from the payment terminal to the payment processing center/bank through the agreement. Vulnerabilities.
Internal vulnerability
Locally, researchers have found that a large percentage of German payment programs use the ZVT protocol, which has long been exposed to simple sniffing attacks, allowing attackers to intercept credit card data.
Moreover, the process of reading the password of the credit card by the PoS machine and transmitting the response information to the cash register after obtaining the transaction authorization is also the responsibility of the ZVT protocol.
Although the above steps were completed by encryption, the researchers found that the POS manufacturer saved the encryption key in the PoS machine and repeatedly used the same key at the same payment point.
This means that if an attacker can invade a PoS terminal and propose an encryption key, then he has the ability to read encrypted traffic in the store's local LAN, including the bank card number and password.
External vulnerability
Unfortunately, communication between the PoS terminal and the payment processing center/bank is also problematic. The protocol used to exchange data between the two parties is a variant of ISO 8583 (Financial Transaction Card Original Message - Exchange Message Specification), which is called Poseidon in Germany and other countries, but there is an authentication defect in this variant. Similar to previous internal vulnerabilities, PoS manufacturers also use encryption keys to encrypt information exchanged with the outside world. This key will also be present in the PoS device with very few changes. Therefore, using the same pos machine in the same store, the same key is used repeatedly.
Experts at the Security Research Lab talk about the dangers of using Poseidon encryption keys in multiple payment systems: "Attackers can get a refund, or print multiple mobile phone recharge cards, and the cost is paid by the merchant."
Researchers at the Safety Lab decided to make a concrete presentation at the 32nd Chaotic Communications Conference (32C3) in Hamburg on December 27. 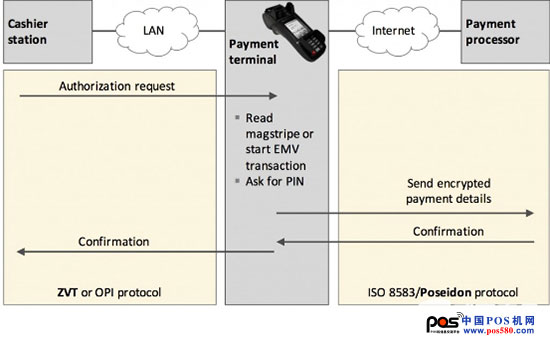
The German payment system mainly uses the ZVT and Poseidon payment protocols, which are at risk for the same reason: they all share keys in many devices. So it is important for each terminal to deploy a separate key, which also makes the payment system more resistant to fraud.